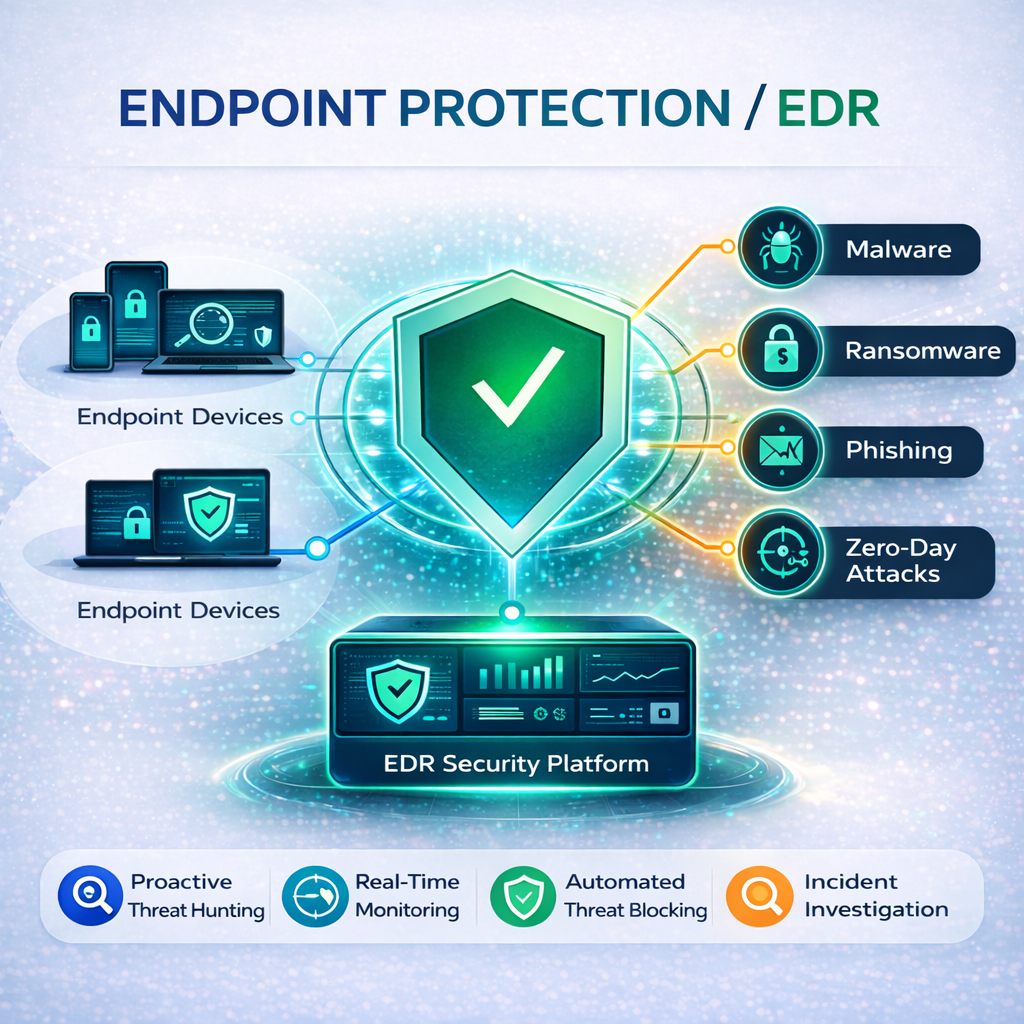
Endpoint Protection / EDR
-
Continuously monitors every endpoint for ransomware, zero-day exploits, fileless attacks, and suspicious behavior using behavioral analytics, not just known signatures. When an unknown executable requests runtime privileges, it's automatically contained in an isolated environment that has no access to your host system's resources or user data, preventing lateral movement across your network before damage can occur.
-
When a threat is identified, MurMur doesn't wait for a human analyst. Compromised endpoints are instantly isolated, malicious processes are terminated, and affected files are quarantined, all automatically. Unauthorized changes made by malware are reverted, and encrypted files can be rolled back to their pre-attack state. Detection to containment happens in under one second, not hours.
-
Every process creation, registry modification, network connection, memory access, and privilege escalation is recorded and tracked across all endpoints in real time. When an incident occurs, security teams get a complete attack chain reconstruction with process tree visualizations showing exactly where the attack began, how it moved, and what it touched, eliminating guesswork and reducing investigation time from days to minutes.
-
anage every device from a single dashboard; Windows, macOS, Linux, iOS, Android, and cloud workloads. Deploy the lightweight agent in minutes via GPO, Intune, Jamf, or a one-line command with zero disruption to users. Integrates with your existing SIEM, SOAR, and threat intelligence platforms for centralized visibility. Whether you're protecting 10 endpoints or 10,000, one console handles it all.
MUR
Schedule A Call Now!